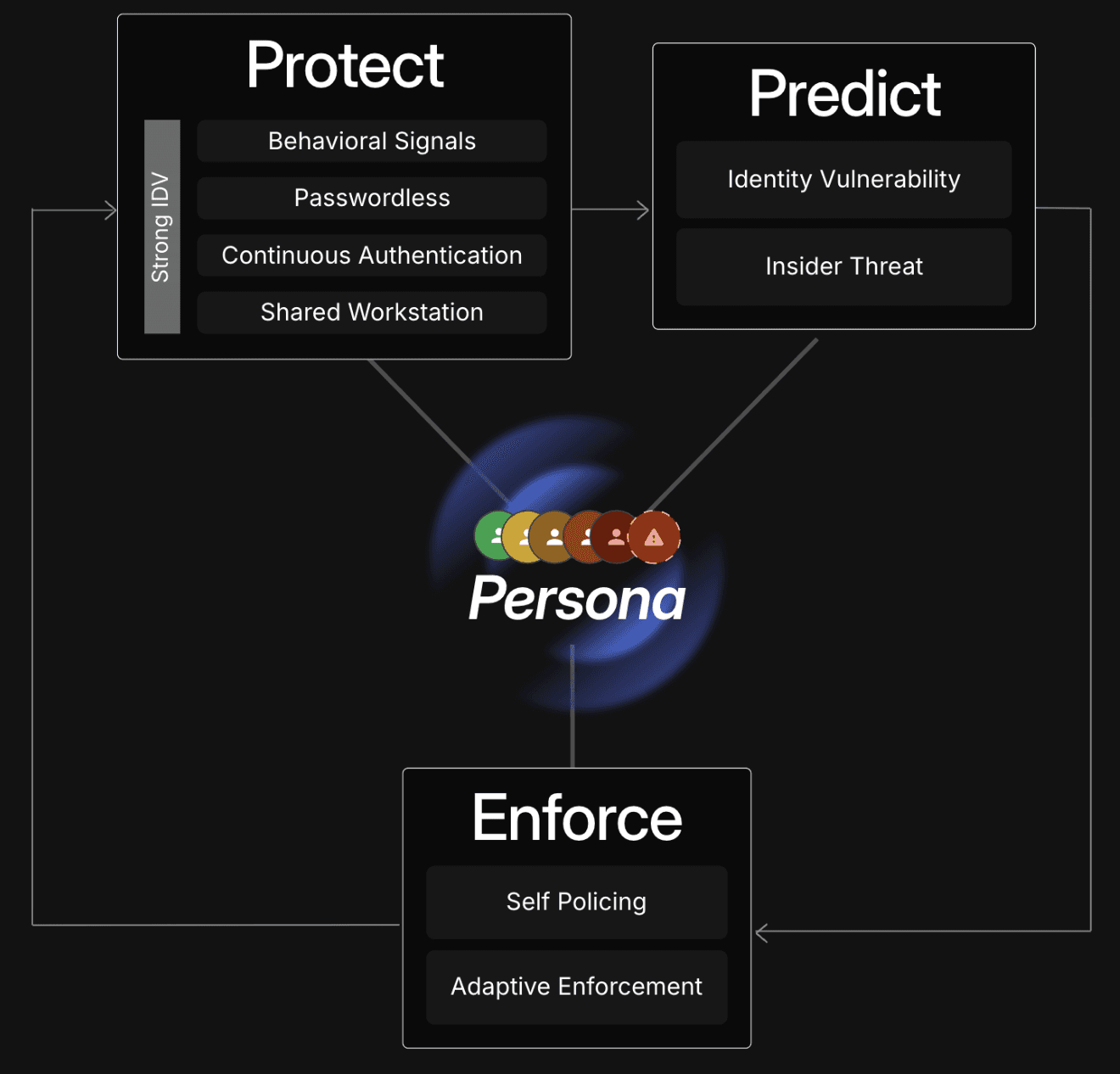
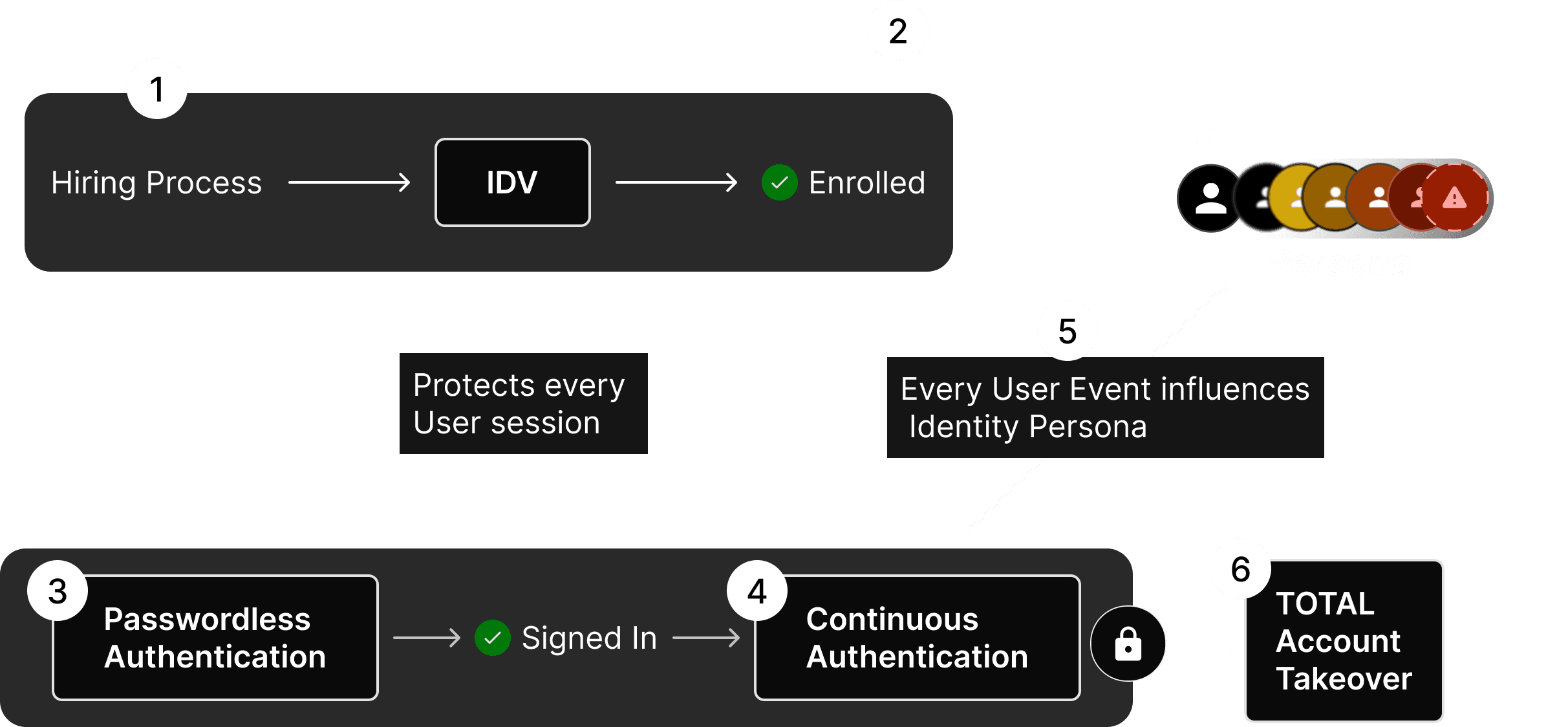
TruU’s Proprietary Identity Persona™
TOTAL understands who is acting — not just what they’re doing
TOTAL builds 72-dimension Personas based on cross-domain principles of behavior and psychology.
TOTAL evaluates the risk of each event in the context of an identity Persona.
Personas are continually tested for drift to avert slow moving sophisticated actor and collusion threats.
By setting context, TOTAL reduces false negatives (prevents breaches) & false positives (reduces noise).
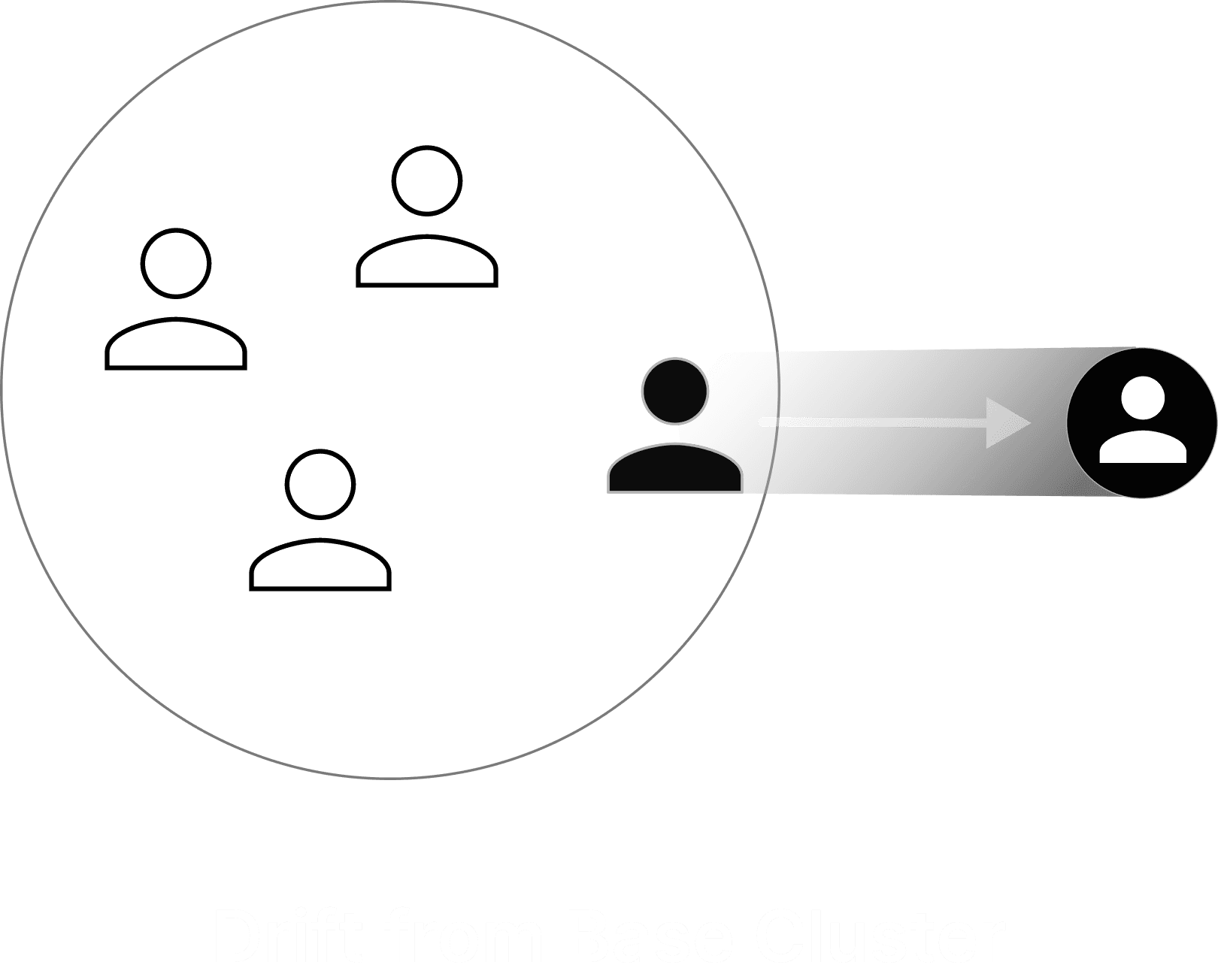
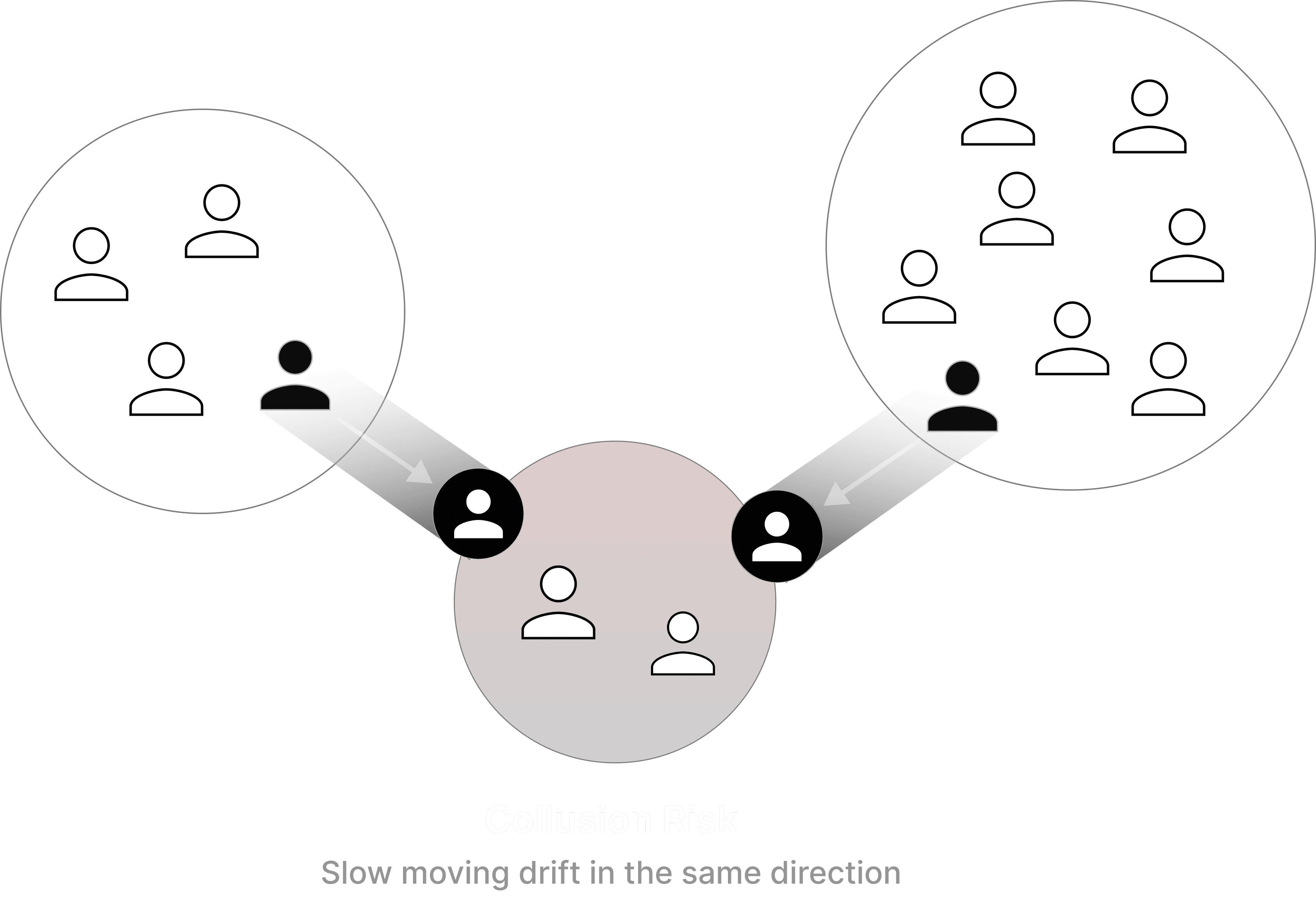
TruU’s Proprietary Persona Cluster™

Several ”like-cyber-minded” Personas are clustered together using TruU's proprietary algorithm.
Our clustering algorithm enables continuous drift measurements to estimate both threat & vulnerability risk right from Enrollment.
Clustering and drift measurements let TOTAL work with a large stage of risk-actors so even the faintest threats can be monitored in nascent stages
How TOTAL catches Insider Threats
LEVEL 1
Explicit Rule Violations
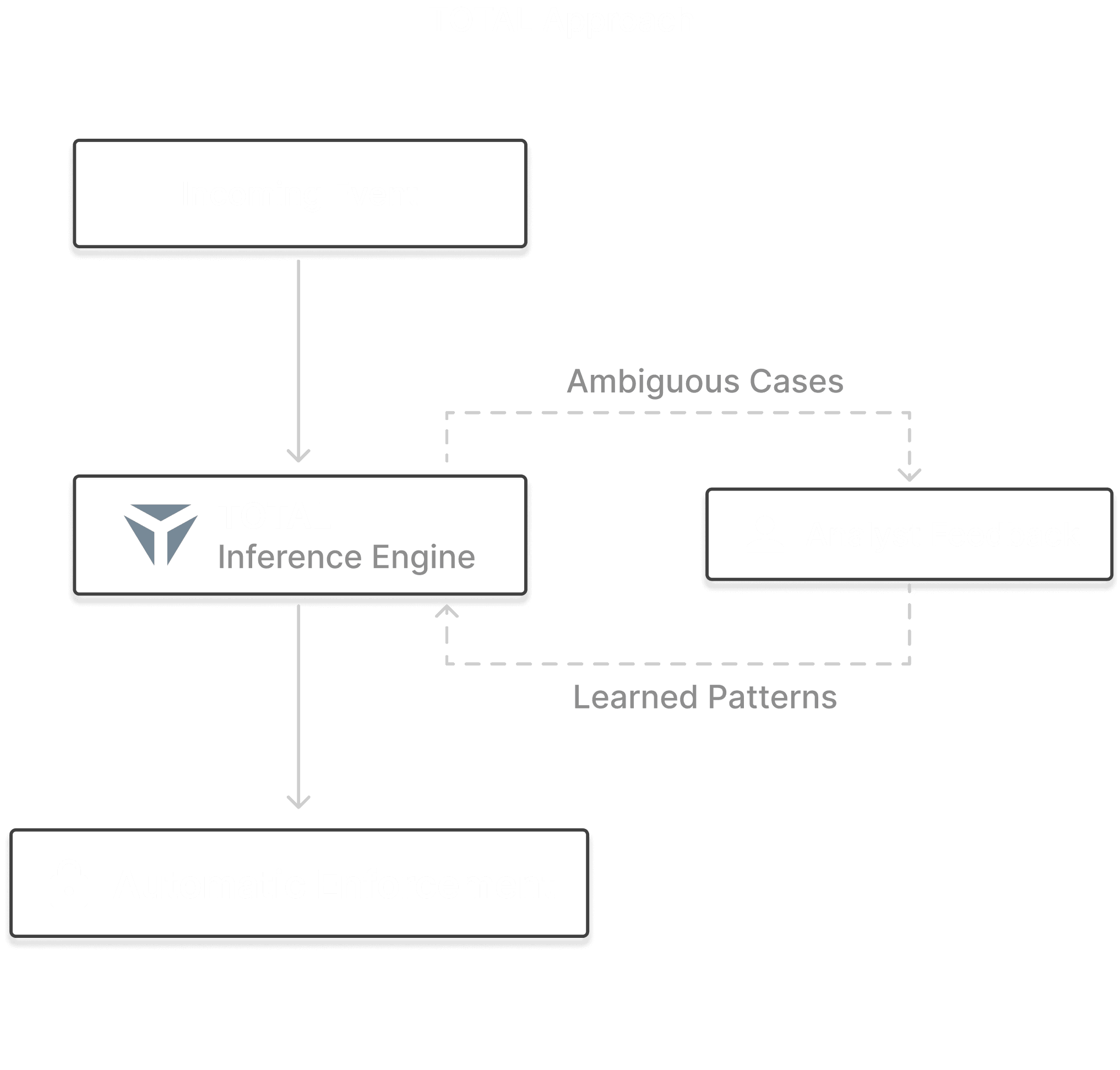
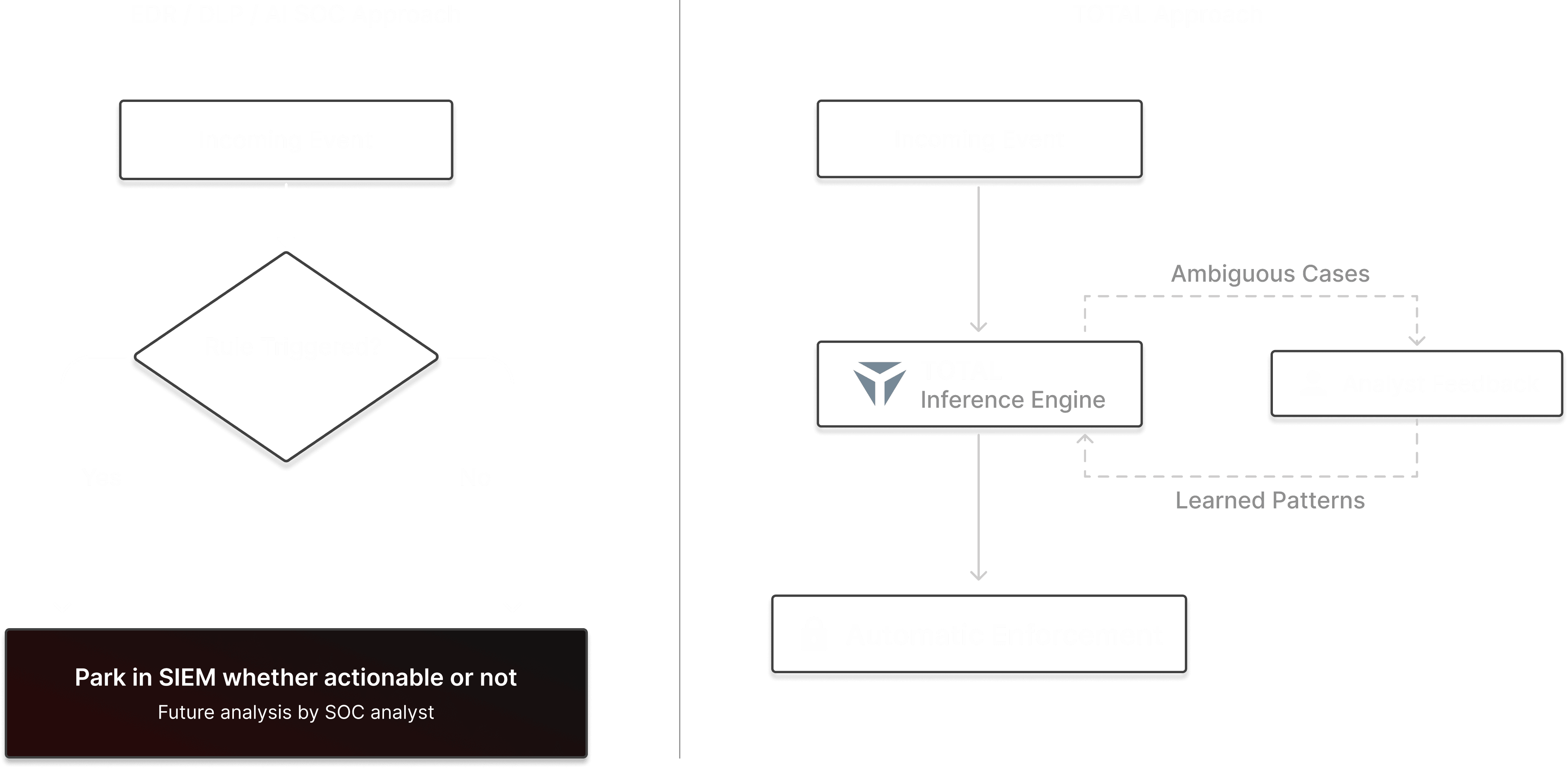
Simple EDR/DLP products miss sophisticated threats that do not violate hard-coded rules and persist inside your cyber infrastructure forever. These rule-based systems also generate considerable false positives that flood the SOC with alerts.
To reduce false positives, TOTAL continuously learns from every reviewed alert and confirmed threat. With each analyst decision, the prediction engine grows smarter, reducing noise and automatically enforcing action on known threat patterns. Over time, the result is a SOC that’s leaner, faster, and more intelligent.
LEVEL 2
Contextual Abuse of
Legitimate Access
With traditional tools, events are forwarded to the SIEM and investigated retrospectively, after the attack chain has already begun.
TOTAL assesses risk in real time by applying Persona context.
LEVEL 3
Complex Sophisticated
& State Actor Attacks
Persona, Clusters & Drift are TruU Proprietary foundations of predicting and thwarting the type of attacks we read about in the news.
A drift from base Persona & a drift from Cluster is measured – whether slow or fast. If it exceeds a threshold, the offending identity is put on an internal watchlist.
When two identity Personas drift either in similar or complementary direction, they are put on collusion watchlist.
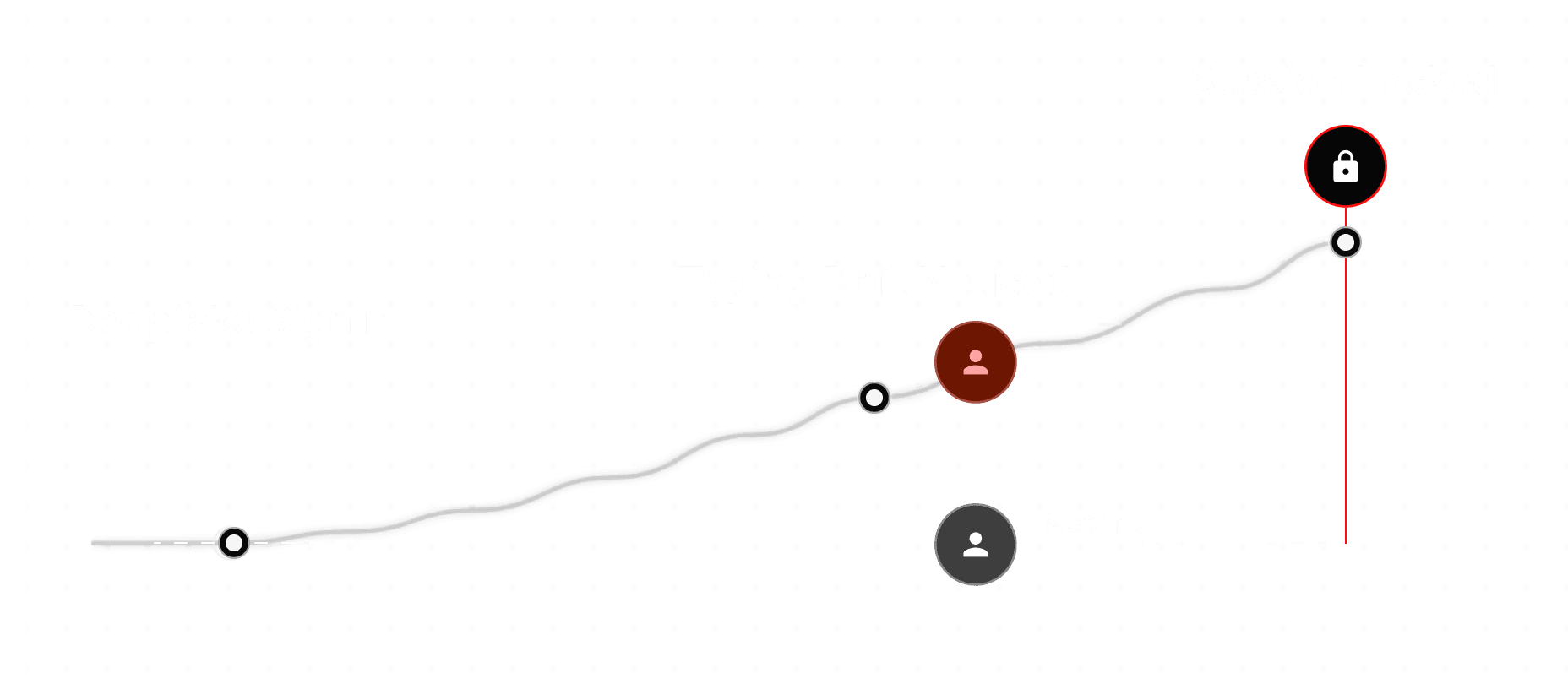
TOTAL Eliminates Account Takeover Risk
LEVEL 1
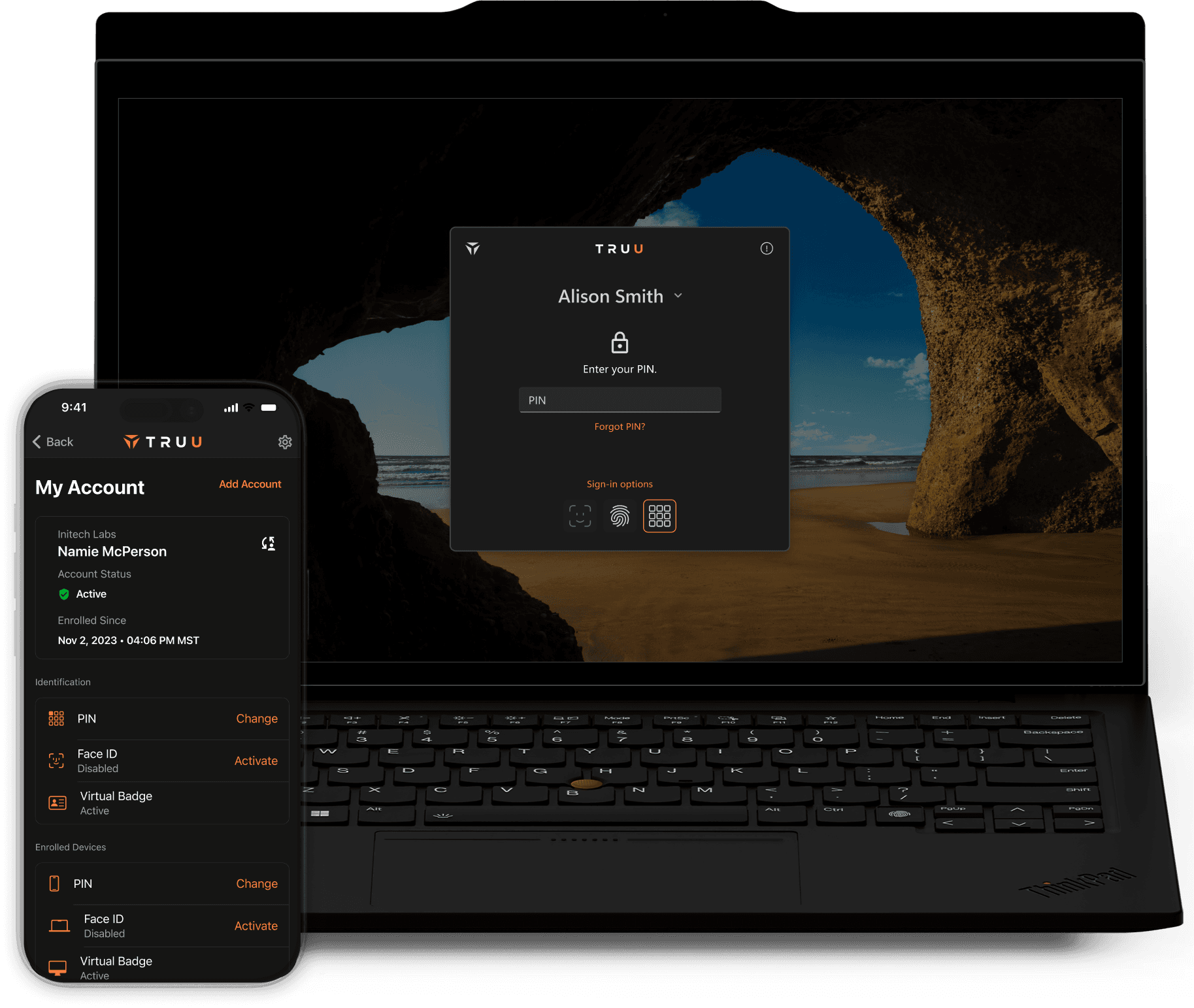
Eliminate the Credential Attack Surface
Every account takeover begins with credential compromise — passwords, tokens, session cookies, and increasingly, stolen or bypassed MFA.
Attackers no longer need to “hack” systems - they phish credentials, intercept MFA codes, deploy MFA fatigue attacks, or leverage adversary-in-the-middle tooling to steal session tokens in real time.
TOTAL Protect neutralizes this attack vector by eliminating the credentials attackers are trying to steal. If credentials cannot be stolen, the ATO chain cannot begin.
LEVEL 2
Human Compromise and AI-Driven Social Engineering
Modern ATO's escalate beyond credential theft. Attackers increasingly target help desks, support workflows, and identity verification processes through social engineering and AI-powered deepfakes.
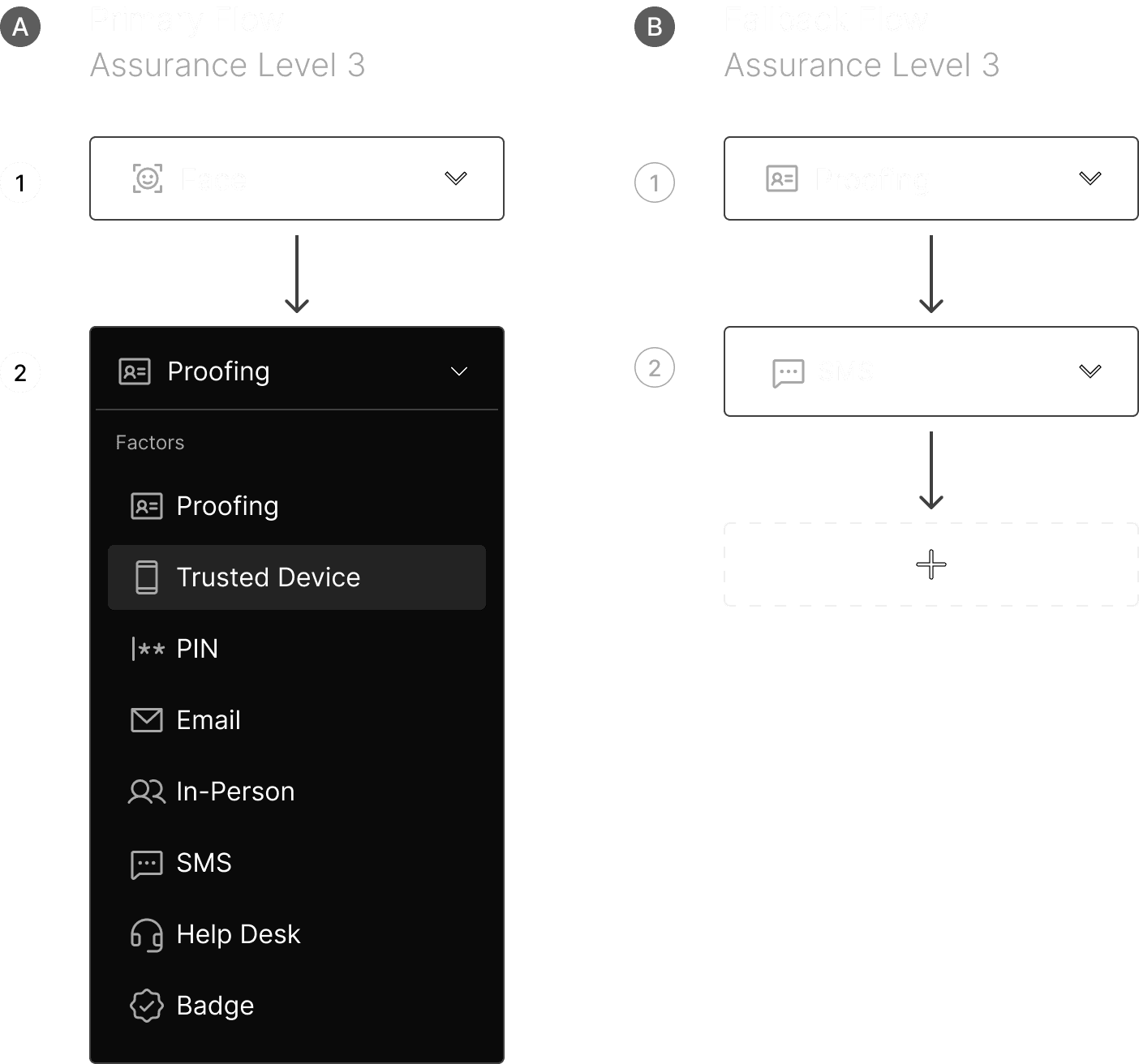
TOTAL IDV addresses this through:
Biometric identity verification
Active liveness detection
AI-driven deepfake detection
Device trust verification
LEVEL 3
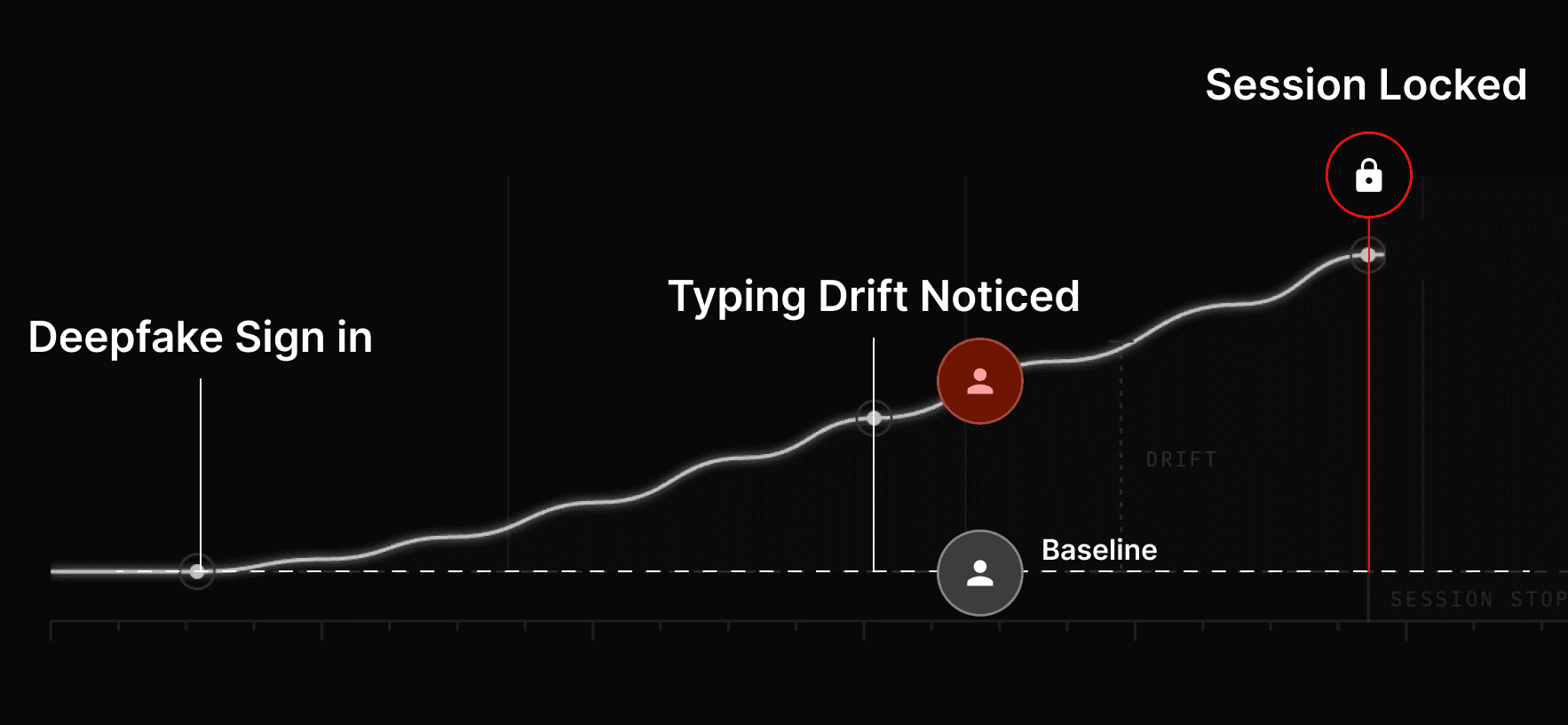
Continuous Persona Integrity Monitoring
Even the most advanced deepfake detection systems can be challenged. This is where TOTAL extends beyond point-in-time identity verification.
TOTAL continuously evaluates the digital persona behind the account in real time. By analyzing behavioral signals and detecting identity drift, TOTAL determines whether the account remains in the control of its rightful owner.